Cybersecurity risks in restaurants: the hidden threats owners miss
Cybersecurity risks in restaurants usually sit in the everyday routines, not the tech stuff. Our blog post this week explains where the real exposure hides and how to reduce it without slowing service. If it feels manageable, that's because it is ... Cybersecurity risks in restaurants can pose hidden threats that owners often overlook, leaving their business vulnerable Most owners don't wake up thinking about cybersecurity risks in restaurants, because the priority is service, margins and keeping the place moving. That's exactly why criminals like the sector: the busiest moments provide the best cover for minor security lapses. The encouraging bit is that the biggest weaknesses can be | ||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
Share the blog love ... | |||||||||||||||||||||||
#CybersecurityRisksInRestaurants #HospitalityIT #POSSecurity #CyberAwareness #DataProtection |
About Wolverton Solutions ... | ||
|
More blog posts for you to enjoy ... | ||
 | Why plain-English IT advice keeps hospitality running smoothly Here's the thing: plain-English IT advice turns tech noise into calm decisions during a shift. It keeps teams aligned during outages, upgrades and busy check-ins. If it's clear, it gets used ...... | |
 | IT in hospitality: why IT fails when you need it most IT in hospitality tends to wobble right when covers are full, and guests are least patient. This breaks down into avoidable patterns: lost orders, slower serving, and frustrated customers. Here's the practical way to think ab... | |
 | Why hospitality businesses feel IT pain more than other industries IT for hospitality businesses takes the hit first because service can't stop while systems recover. When tech stumbles, revenue, reputation, and staff confidence wobble in minutes. The good news is that the right approach tur... | |
 | What are the top IT challenges in the hospitality sector? The right IT system in the hospitality sector is becoming increasingly important as businesses rely more heavily on technology to deliver smooth, efficient and personalised guest experiences. From hotels and restaurants to pu... | |
 | What the hospitality industry gets wrong about IT In the hospitality industry, technology is often treated as a background utility; something that should function quietly and not require attention. On the surface, that seems reasonable. The focus is, after all, on guests, se... | |
 | How IT Failures Turn Into One Star Reviews Overnight In hospitality, reputation is everything. A cafe, restaurant, pub or hotel can spend years building a loyal customer base, only for a handful of negative online reviews to undo that hard work surprisingly quickly. What many h... | |
 | Why ''It's Always Worked Before'' Can Break Hospitality IT Overnight If ''it's always worked before'' is the plan, hospitality IT is already on borrowed time. Demand grows, updates shift, and hardware fades quietly until a busy service exposes the weakest link. A few proactive checks keep chan... | |
 | When the internet goes down: keeping your hospitality venue trading calmly If the internet goes down, the venue doesn't have to. This is a practical, conversational look at what fails first, what still works, and how to plan resilience without drama. The goal is steady service, even on a bad connect... | |
Other bloggers you may like ... | ||
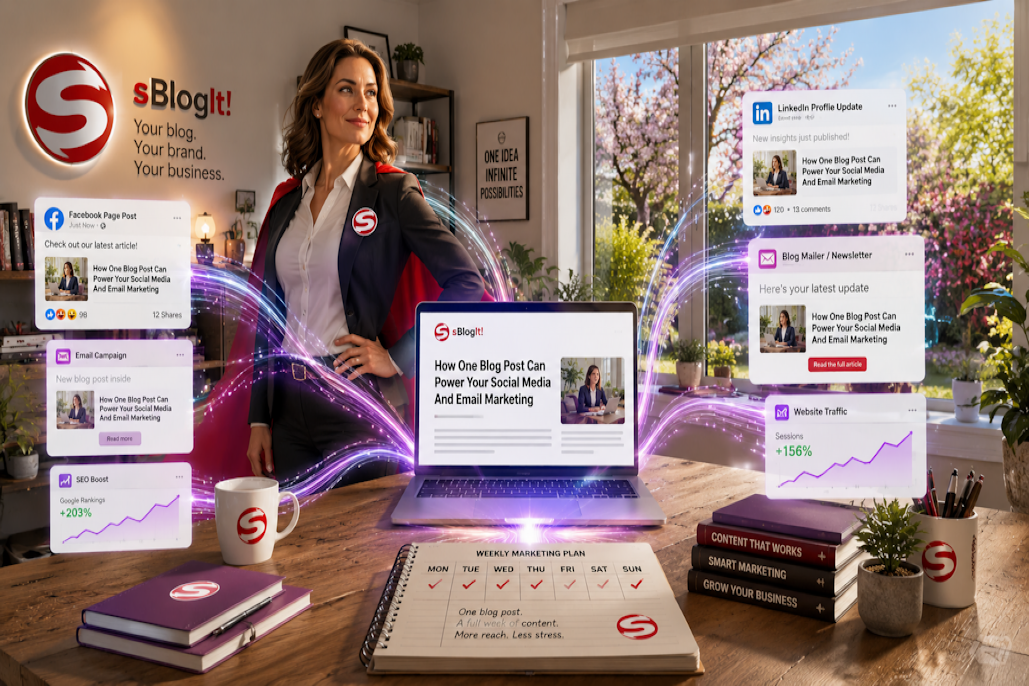 | How one blog post can power your social media and email marketing Posted by Steffi Lewis on https://www.sblogit.com Many small business owners think they need a constant stream of fresh ideas to keep their marketing active. In reality, one good blog post can often p ... | |
 | Why Some Network Groups Flounder Posted by Jacky Sherman on https://www.jackysherman.com If you're running your own small business, sooner or later, you will go networking. And when you do, you will quite quickly discover that some network ... | |
 | Contractor accommodation in Milton Keynes for modern business stays Posted by Emily Freeman on https://blog.shortstay-mk.co.uk Contractor accommodation in Milton Keynes suits teams that need more than a hotel room. It offers space, privacy, parking, and practical comforts to k ... | |
 | Mentors and goal buddies: how they help you reach your goals Posted by Dave Cordle on https://blog.davecordle.co.uk Mentors and goal buddies can make your ambitions clearer and more achievable. You get advice, perspective and accountability, and you stay on track wh ... | |



